Hi everyone,
First of all, a big thank you to this amazing community for your continuous support and the wealth of knowledge shared here. It's truly appreciated!
We are currently using osTicket version 1.18 installed on an Azure B2MS VM. The system is connected to a MySQL Flexible Server instance via a private VNET.
Previously, we successfully configured a dedicated mailbox on Microsoft 365 using oAuth2 registration. However, recent changes on Microsoft’s side seem to have disrupted our setup. Now, we’re completely locked out of the system as both agents and administrators cannot access it due to email-based MFA being enabled (emails with token are not beeing sent).
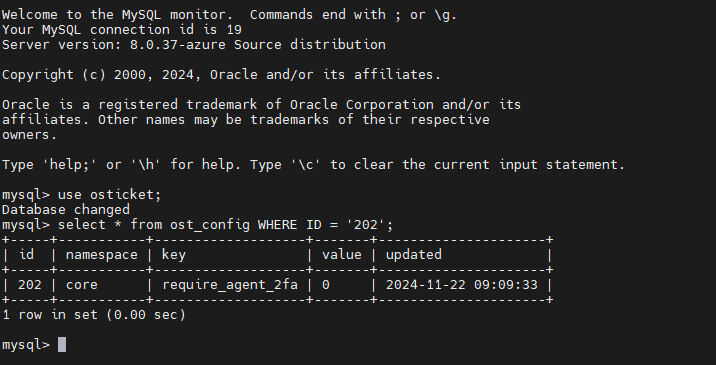
We have tried following some suggestions found in this forum, such as modifying the 2FA settings directly in the database. Unfortunately, this approach has not worked for us. After every configuration attempt, we have restarted both the VM running osTicket and the Azure-managed MySQL instance, but the issue persists.
Additionally, we’ve noticed that the system is no longer polling the dedicated M365 mailbox or opening tickets from incoming emails.
We are including a screenshot of the current configuration for reference.
Could we have missed something? Is there anything else we should do to regain access to the system? Your guidance would be greatly appreciated!
Thanks in advance for your help!